One-Time Pad
The only cipher proved mathematically unbreakable — and nearly impossible to use correctly
Why This Matters
The only cipher mathematically proven to be unbreakable. Claude Shannon’s 1949 proof of its perfect secrecy is a cornerstone of information theory — and the VENONA project showed exactly what happens when its rules are violated.
Frank Miller described a one-time pad system in 1882. Gilbert Vernam patented a teletype version in 1917. But it was Claude Shannon who proved in 1949 that the OTP achieves perfect secrecy — ciphertext reveals absolutely nothing about the plaintext to an attacker with unlimited computing power.
The VENONA project showed exactly what happens when the rules are broken: Soviet signals officers reused key pages under WWII supply pressure. The NSA decoded thousands of messages and identified Julius Rosenberg, Klaus Fuchs, and other Soviet agents.
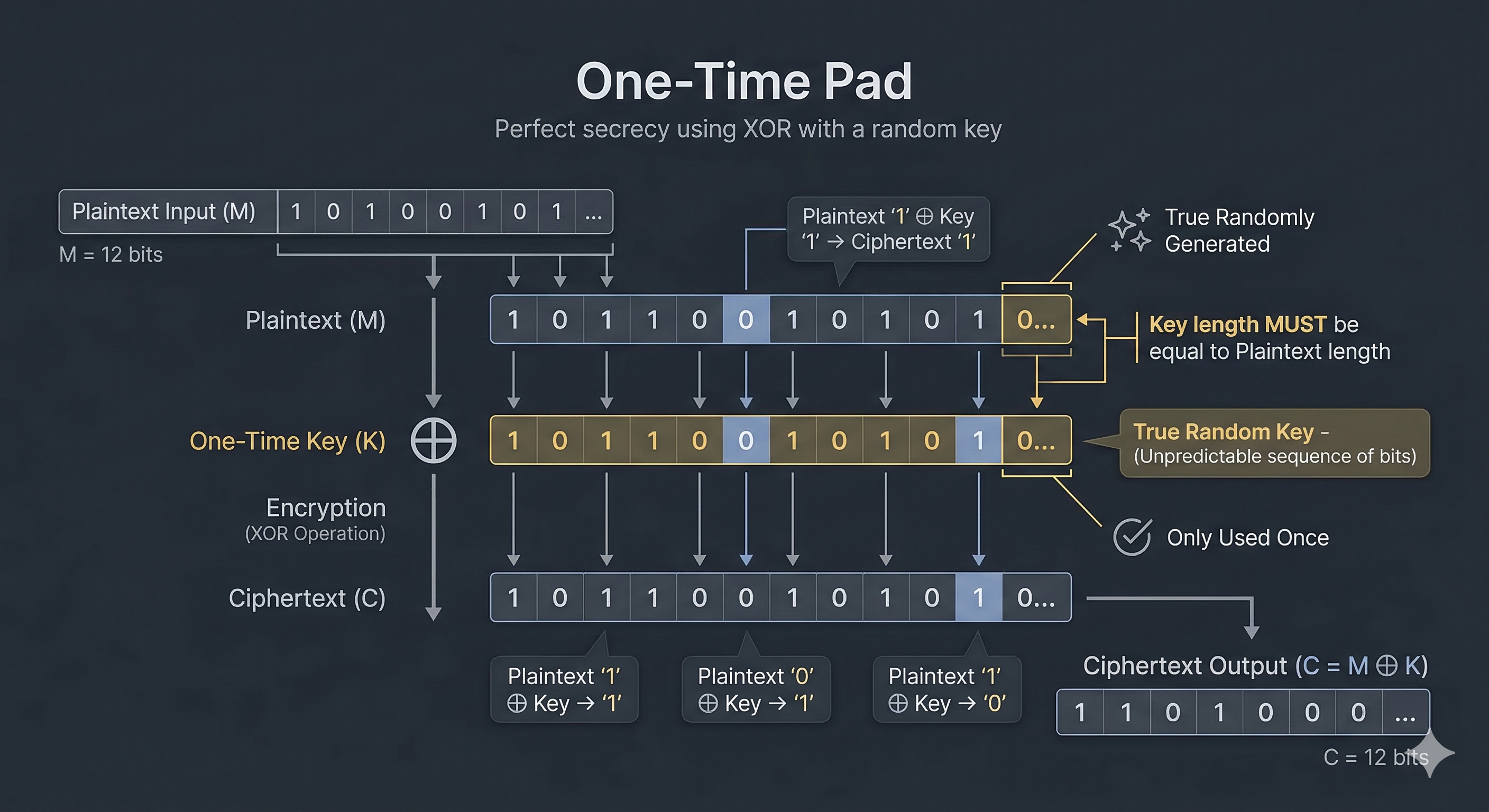
Encryption: C = P XOR K Decryption: P = C XOR K Example: Plain: H E L L O = 07 04 11 11 14 Key: X M C K L = 23 12 02 10 11 (random) Cipher: 30 16 13 21 25 mod 26 = E Q N V Z Four requirements for perfect secrecy: 1. Key must be truly random (not pseudorandom) 2. Key must be as long as the message 3. Key must never be reused 4. Key must be kept secret Violate any condition → security collapses
Shannon's proof (1949): For any ciphertext C and any possible plaintext P, P(plaintext=P | ciphertext=C) = P(plaintext=P). The ciphertext provides zero information about the plaintext. An attacker with unlimited computing power cannot do better than random guessing.
C1 XOR C2 = P1 XOR P2. If two messages are encrypted with the same key, XORing the ciphertexts eliminates the key and produces the XOR of the plaintexts. With enough crib-based guessing, both plaintexts can be recovered. The Soviets reused pads in 1942-1943 under wartime supply pressure — giving the NSA its entry point.
| Concept from One-Time Pad | Modern Evolution |
|---|---|
| Perfect secrecy (Shannon, 1949) | Information-theoretic vs computational security: the fundamental distinction |
| XOR as cipher operation | Every modern stream cipher uses XOR with a keystream |
| Key = message length | The impracticality drove development of public-key cryptography (RSA, DH) |
| Key reuse is catastrophic | Nonces, IVs, session keys: modern protocols prevent key reuse by design |
Message: A T T A C K (6 letters) As numbers (A=0): 0 19 19 0 2 10 Random key: 7 14 3 8 25 16 (from true random source — dice, radiation, etc.) Encrypt — add mod 26: A(0) + key(7) = 7 mod 26 = 7 → H T(19) + key(14) = 33 mod 26 = 7 → H T(19) + key(3) = 22 mod 26 = 22 → W A(0) + key(8) = 8 mod 26 = 8 → I C(2) + key(25) = 27 mod 26 = 1 → B K(10) + key(16) = 26 mod 26 = 0 → A Ciphertext: H H W I B A Decrypt — subtract mod 26: H(7) − key(7) = 0 mod 26 = 0 → A ✓ H(7) − key(14) = −7 mod 26 = 19 → T ✓ Why unbreakable: HHWIBA could decrypt to any 6-letter message with some key. Without the key, all plaintexts are equally likely.
- Enigma Machine — Rotor cipher that traded perfect secrecy for practicality
- Lorenz Cipher — XOR-based teleprinter cipher inspired by OTP principles
- Vigenère Cipher — Repeating-key polyalphabetic: what happens when the key is shorter than the message
| Exhibit | 26 of 40 |
| Era | 1882 · Theoretical |
| Security | Provably Secure* |
| Inventor | Frank Miller (1882) · Vernam (1917) · Shannon (1949) |
| Year | 1882 / 1917 |
| Key Type | Random key same length as message (used once) |
| Broken By | Never — if rules followed. VENONA: key reuse exploitation |