Lorenz Cipher
Hitler's strategic cipher — broken by a mistake, and it built the world's first computer
Why This Matters
The Lorenz SZ40/42 protected Hitler’s highest-level strategic communications. Breaking it — without ever seeing the machine — led Bill Tutte to reconstruct its logic and Tommy Flowers to build Colossus, the world’s first programmable electronic computer.
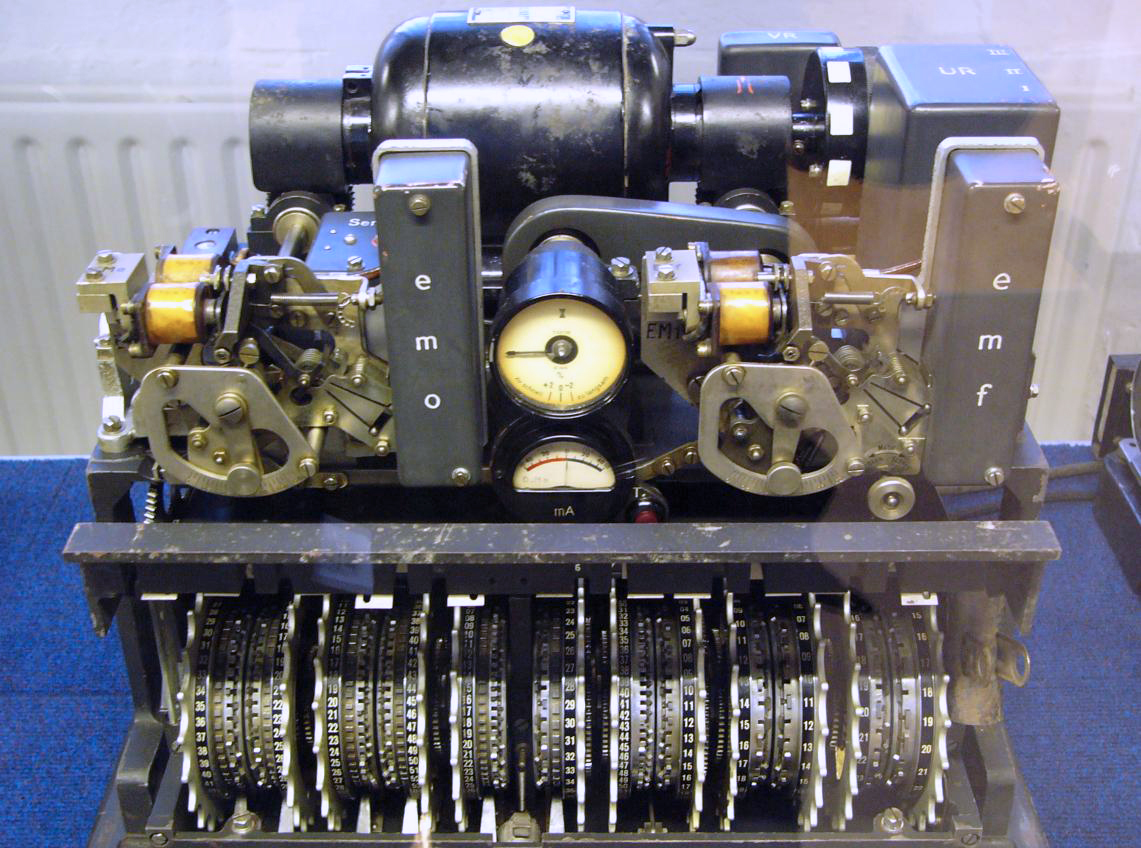
While Enigma protected German field communications, the Lorenz SZ40/42 protected Hitler's strategic communications to his senior commanders. Where Enigma was a hand-operated cipher machine, Lorenz was a fully automatic teleprinter attachment — messages fed in on paper tape, encrypted output punched automatically.
On August 30, 1941, a German operator sent a 4,000-character message, received a request to resend, and sent it again — with the same settings but slightly different plaintext (abbreviating some words). This catastrophic procedural error gave Bletchley Park cryptanalyst Bill Tutte enough to reconstruct the entire Lorenz cipher structure without ever seeing the machine. Tommy Flowers then built Colossus to automate the attack.
Lorenz SZ42 used 12 cipher wheels:
5 Chi (χ) wheels: key stream
5 Psi (ψ) wheels: irregular key
2 Motor wheels: control Psi movement
Encryption: XOR operations on 5-bit
teletype characters (Baudot code)
C = P XOR χ-stream XOR ψ-stream
Wheel pin counts: 41,31,29,26,23,
43,47,51,53,59,
61,37
Total period: LCM of all wheels
= astronomically large — never repeats in practice
Both ran in parallel through the war, and both lived in the same Bletchley campus. They are the same family of problem solved with very different ambitions — and they failed for very different reasons.
| Enigma (1923 / field) | Lorenz SZ40/42 (1940 / strategic) | |
|---|---|---|
| Who used it | Army, Navy, Luftwaffe — every front-line unit | OKW ↔ Hitler & senior commanders only |
| Operator model | Hand-typed, lamp-board readout, telegraph the result | Inline teleprinter attachment — paper tape in, encrypted tape out, fully automatic |
| Cipher primitive | Polyalphabetic substitution via 3–4 stepping rotors + reflector + plugboard | Vernam XOR of 5-bit Baudot characters with a 12-wheel pseudo-random keystream |
| Key space | ≈ 1.6 × 1020 (with plugboard) | ≈ 1.6 × 1019 wheel period — but reusable settings, not a one-time pad |
| Fatal weakness | Reflector → no letter encrypts to itself → cribs eliminate placements | Reusing a wheel setting collapses two messages into a depth (PA ⊕ PB) |
| What broke it | Cribs + electromechanical Bombe (Turing, Welchman, 1940) | One operator's depth + Tutte's wheel reconstruction (1942) + Colossus (1944) |
| What it built | Cryptanalysis as an industrial discipline — 10 000 staff, daily key recovery | Programmable electronic computing — Colossus is the direct ancestor of every machine you own |
| Modern echo | Side-channel and operational security still beat strong primitives | Nonce reuse on AES-GCM, IV collisions on WEP — the depth attack, unchanged |
If Enigma is the canonical example of strong primitive defeated by usage patterns, Lorenz is the canonical example of strong primitive defeated by a single repeated key. Eight decades later, both lessons are still being relearned in production code.
The operator's mistake (same settings, similar plaintext) created a "depth" — two messages XORed together give P1 XOR P2 (the keys cancel). From this, Tutte deduced the complete wheel structure without seeing the machine — a cryptanalytic feat considered one of the greatest intellectual achievements of WWII. Colossus (1943) automated the wheel-setting problem, running at 5,000 characters per second.
The depth attack, in your browser
Two ciphertexts encrypted under the same Lorenz keystream. XOR them together and the keystream cancels — what remains is P1 ⊕ P2, a "depth" that leaks structure. Drag a guessed crib across the depth: where the result reads as English, the crib is correct in one message and the slice you recover is the matching plaintext from the other.
What you just witnessed: a single repeated key turns a Vernam cipher into a paper exercise. The keystream cancels in the XOR, the plaintexts leak through each other, and one good crib unzips both messages. Bill Tutte recovered the entire 12-wheel structure of Lorenz from one 4 000-character depth — without ever seeing the machine.
Why this still matters. Every modern stream cipher — RC4, ChaCha20, AES-CTR, AES-GCM — is a Vernam construction with a generated keystream. The depth attack you just ran is bit-for-bit identical to the WEP IV-collision attack that broke Wi-Fi (2001), the nonce-reuse attack on AES-GCM (still rediscovered in audits), and the forbidden-attack on TLS 1.2 GCM cipher suites. The cryptography textbooks call it two-time pad. The wartime cryptanalysts called it depth. The mistake is the same mistake.
| Concept from Lorenz Cipher | Modern Evolution |
|---|---|
| Wheel-based keystream generator | Linear Feedback Shift Registers (LFSRs): the direct descendant of rotor-based keystreams |
| XOR teleprinter encryption | Vernam cipher: XOR is the foundation of all stream cipher design |
| Breaking it built Colossus | The needs of cryptanalysis drove the invention of programmable computing |
| Depth attack on reused settings | Nonce reuse attacks: identical to the Lorenz depth attack, still relevant today |
Plaintext character: H
Baudot (ITA2) code: 10100 (5-bit)
Wheel outputs at current position:
χ wheels (5 bits): 0 1 1 0 1
ψ wheels (5 bits): 1 1 0 1 0
Step 1 — XOR with χ stream:
Plaintext: 1 0 1 0 0
χ stream: 0 1 1 0 1
Result: 1 1 0 0 1
Step 2 — XOR with ψ stream:
Intermediate: 1 1 0 0 1
ψ stream: 1 1 0 1 0
Ciphertext: 0 0 0 1 1 = Baudot "D"
After each character:
• All 5 χ wheels advance one position
• Motor wheels decide whether ψ wheels step
(irregular motion = extra security)
With all 12 wheels: period before repetition
≈ 1.6 × 10¹⁹ characters — effectively infinite- Enigma Machine — The field-level rotor cipher Lorenz outranked
- One-Time Pad — Lorenz used XOR like a OTP but with a periodic key
- VIC Cipher — Cold War hand cipher that resisted machine analysis
| Exhibit | 28 of 40 |
| Era | WWII · Germany · 1940 |
| Security | Broken |
| Inventor | Lorenz AG · German High Command |
| Year | 1940 |
| Key Type | 12-wheel teleprinter cipher (Vernam-based) |
| Broken By | Bill Tutte · Known plaintext · Colossus computer (1943) |