Vigenère Cipher
"Le chiffre indéchiffrable" — 300 years of misplaced confidence
Why This Matters
Called "le chiffre indéchiffrable" for nearly 300 years, the Vigenère cipher introduced polyalphabetic substitution — the idea that a single plaintext letter could encrypt to many different ciphertext letters. Its eventual defeat spawned the entire field of modern cryptanalysis.
Giovan Battista Bellaso described the cipher in 1553, but it was misattributed to Blaise de Vigenère — who described a different, stronger cipher — and the name stuck. By the 17th century it was the standard diplomatic cipher of European courts. French cryptographers called it "le chiffre indéchiffrable" — the unbreakable cipher.
It remained unbroken for nearly 300 years. Charles Babbage cracked it in the 1850s but kept his method secret. Friedrich Kasiski published independently in 1863, ending the myth forever.
Civil War use: The Confederate Signal Corps adopted the Vigenère as "the government cipher" — apparently unaware that it had already been publicly broken. Union cryptanalysts read Confederate dispatches throughout the war. Real Confederate keywords: Manchester Bluff, Complete Victory, Come Retribution.
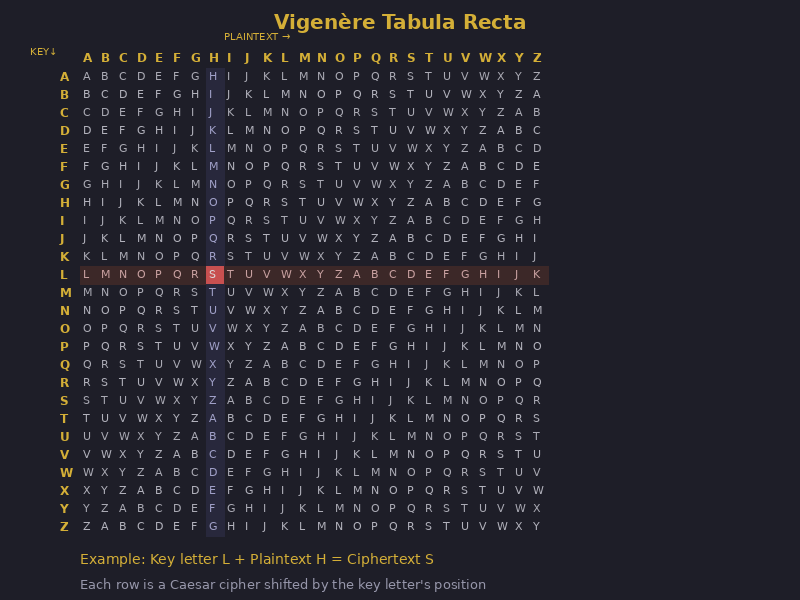
The Vigenère uses a 26×26 "tabula recta" — a grid of all 26 Caesar shifts. The keyword determines which row to use for each letter:
- Write the keyword repeatedly above the plaintext
- For each plaintext letter, find its column in the tabula recta
- Find the row corresponding to the key letter above it
- The intersection is the ciphertext letter
Key: L E M O N L E M O N L E Plain: A T T A C K A T D A W N Cipher: L X F O P V E F R N H R Formula: C = (P + K) mod 26
The same plaintext letter encrypts differently each time — A becomes L, then M, then O depending on which key letter is above it. This completely defeats simple frequency analysis.
Tabula Recta — Hover over cells to explore
When the same plaintext segment aligns with the same key segment, it produces identical ciphertext. Search for repeated 3+ letter sequences in the ciphertext. The distances between repetitions are likely multiples of the key length. Find the GCD of all distances — that's the key length.
Once the key length is known, split the ciphertext into N groups (N = key length). Each group was encrypted with the same Caesar shift. Apply frequency analysis to each group independently to recover the key letter for that position.
The fatal flaw: The keyword repeats. Every 5 letters (for a 5-letter key), the same substitution alphabet is used again. This periodicity is invisible to the eye — but mathematically detectable with enough ciphertext.
| Vigenère Concept | Modern Evolution |
|---|---|
| Multiple alphabets (key-dependent shift) | Stream ciphers: ChaCha20 generates a different keystream byte for every position |
| Repeating key → detectable periodicity | Modern keystreams never repeat within a session (nonce + counter prevents this) |
| Key length determines security | AES-256 uses a 256-bit key — guessing it requires 2²⁵⁶ operations |
| XOR-equivalent operation | All modern stream ciphers use XOR: C = P ⊕ keystream |
Paste Vigenère ciphertext. The tool finds repeated sequences and estimates the key length.
This is a real fragment from the Confederate Civil War cipher system. Key length: 15 letters.
Key: COMPLETEVICT… (15 letters)