Monoalphabetic Substitution
26! possible keys. Zero security.
Why This Matters
Despite having 26! (≈ 4×10²⁶) possible keys, monoalphabetic substitution was permanently broken in 850 AD when Al-Kindi of Baghdad invented frequency analysis — the first general-purpose cryptanalytic technique and one of the most important breakthroughs in the history of cryptography.
Monoalphabetic substitution ciphers — where each letter maps permanently to another letter or symbol — are among the oldest cryptographic techniques. They appear in ancient Hebrew texts (the Atbash cipher), Roman inscriptions, and medieval manuscripts. The sheer number of possible keys (26! ≈ 4×10²⁶) made cryptographers believe they were unbreakable.
That belief shattered in 850 AD when Al-Kindi of Baghdad wrote A Manuscript on Deciphering Cryptographic Messages — a nine-page treatise that introduced frequency analysis and rendered every monoalphabetic cipher permanently insecure.
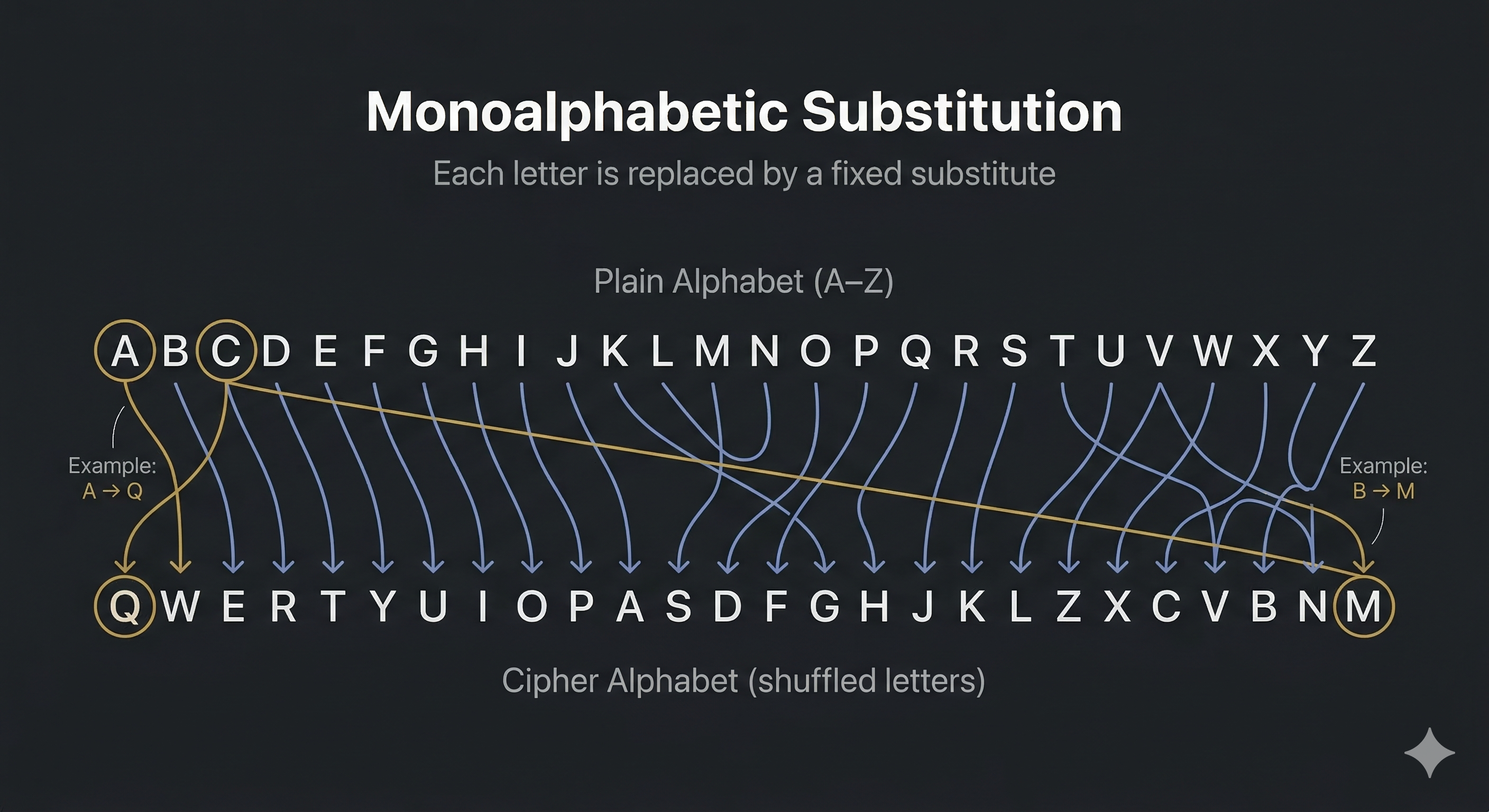
Replace each plaintext letter with a fixed ciphertext letter according to a secret permutation table. The same letter always maps to the same symbol.
Plain: ABCDEFGHIJKLMNOPQRSTUVWXYZ Cipher: QWERTYUIOPASDFGHJKLZXCVBNM HELLO → ITSSG
With 26! ≈ 4×10²⁶ possible keys, brute force is impossible. But the key is irrelevant — the statistical structure of English leaks through every substitution.
In English, E appears ~12.7% of the time, T ~9.1%, A ~8.2%. Because monoalphabetic ciphers map each letter to exactly one symbol, these frequencies are perfectly preserved. Count ciphertext symbols. The most frequent is almost certainly E. The second is T. Map frequencies to expected values, use word patterns (THE, AND, IS) to confirm, and the key reveals itself.
Why 26! keys doesn't help: The keyspace is astronomically large but the statistical fingerprint of English is inescapable. Key size is meaningless if the ciphertext leaks information about the plaintext.
| Concept from Monoalphabetic Substitution | Modern Evolution |
|---|---|
| Letter permutation | AES S-boxes: fixed non-linear substitution tables that resist frequency analysis |
| Fixed substitution leaks frequency | Shannon's confusion: AES S-boxes designed to resist frequency analysis |
| 26 possible frequency peaks | AES avalanche effect: 1 bit change flips ~half all output bits |
| Exhibit | 03 of 40 |
| Era | Medieval · ~800 AD |
| Security | Broken |
| Inventor | Unknown (ancient practice) |
| Year | ~800 AD |
| Key Type | Full alphabet permutation (26! keys) |
| Broken By | Al-Kindi · Frequency Analysis · 850 AD |