Playfair Cipher
Digraph encryption: Wheatstone's elegant fix for single-letter frequency analysis
Why This Matters
The first practical digraph substitution cipher, Playfair broke the paradigm of single-letter substitution. Used by the British military from the Boer War through WWII, it demonstrated that encrypting letter pairs instead of singles could defeat simple frequency analysis.
Charles Wheatstone devised the Playfair cipher in 1854, and Lord Playfair championed it to British officials who were skeptical of more complicated cryptographic systems. Instead of encrypting one letter at a time, Playfair encrypts pairs of letters. That immediately defeats the single-letter frequency analysis that destroyed Caesar and monoalphabetic substitution.
The British Army used Playfair operationally in the Second Boer War, and British and Commonwealth forces still used variants in both world wars for field traffic. It was fast enough for humans, stronger than earlier substitution ciphers, and compact enough for a pocket notebook.
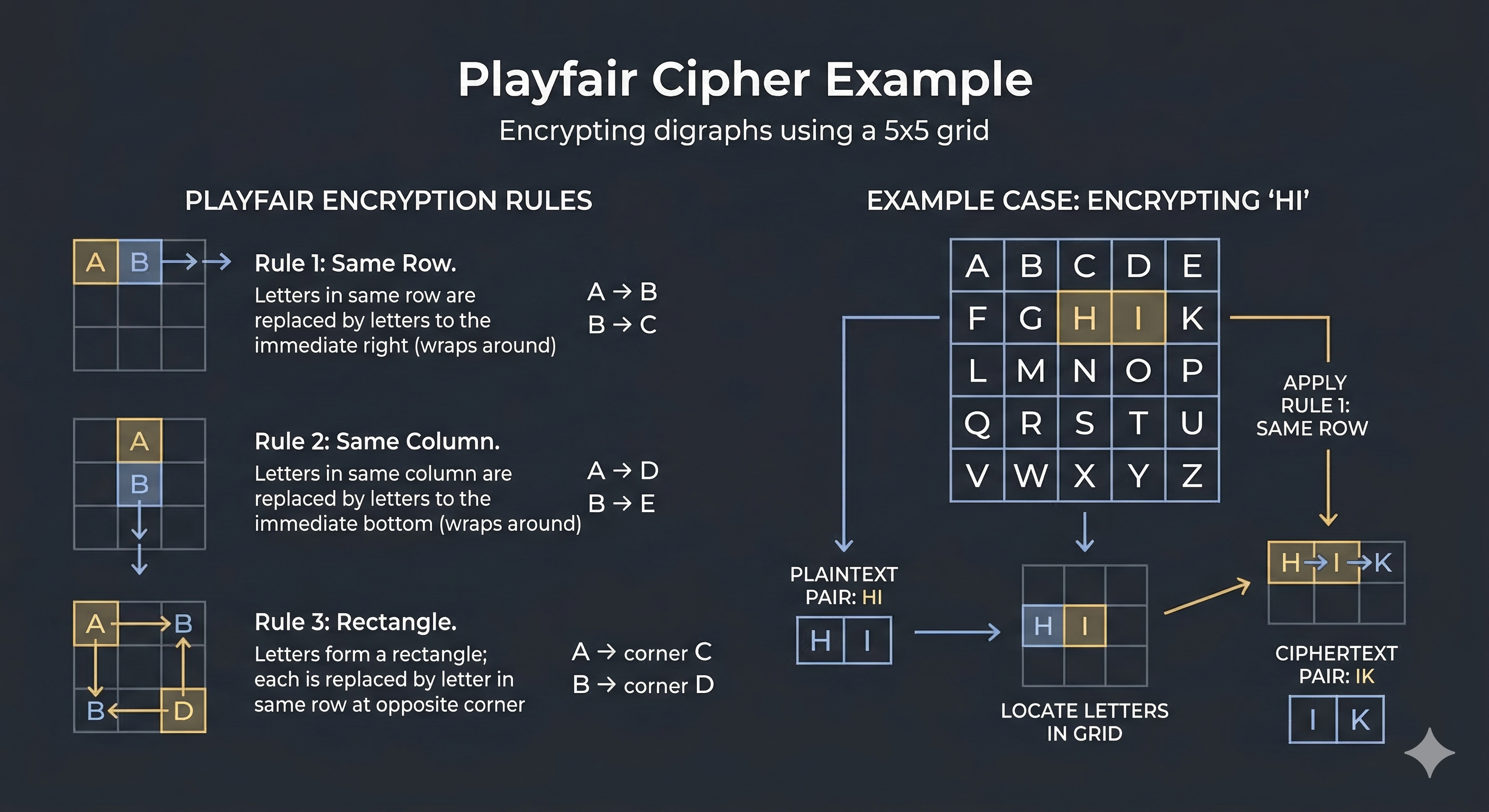
Letters are placed in order, duplicates removed, I/J merged. Remaining letters fill the grid alphabetically.
Split plaintext into digraphs. If a pair repeats a letter, insert X. If the message length is odd, pad the final letter with X.
Each letter shifts one position right, wrapping around.
AR → RM
Each letter shifts one position down, wrapping around.
MC → CE
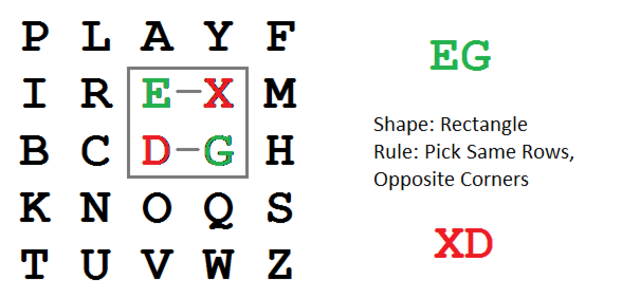
Each letter moves to the other corner of the rectangle, staying in its own row.
HI → BF
Rectangle rule
Playfair hides single-letter frequencies, but it does not hide language. Common English pairs like TH, HE, IN, ER, and AN still leave traces in ciphertext digraphs. Once enough traffic is collected, the key square can be reconstructed by testing candidate arrangements against those digraph statistics.
If the attacker knows even a few plaintext-ciphertext pairs, the key square begins to unravel. Each known digraph pair constrains the positions of four letters at once. With stereotyped openings like "DEAR SIR" or "HEADQUARTERS," the necessary cribs are easy to obtain.
| Playfair Concept | Modern Evolution |
|---|---|
| Encrypt two letters at once | Block ciphers transform many bits together instead of one symbol at a time |
| Position inside a key square matters | AES state matrices mix value and position each round |
| Language patterns survive in ciphertext | Modern ciphers aim for outputs indistinguishable from random noise |
Decrypt this ciphertext using keyword PLAYFAIR:
BM ND ZB ND
Reveal Answer
HE LP ME
Keyword PLAYFAIR produces the square: P L A Y F / I R B C D / E G H K M / N O Q S T / U V W X Z. The digraphs BM ND ZB ND decrypt to HE LP ME XZ — drop the trailing pad X.
| Exhibit | 05 of 40 |
| Era | Victorian · 1854 |
| Security | Broken |
| Inventor | Charles Wheatstone |
| Used By | British field forces |
| Key Type | 5×5 keyword square |
| Broken By | Digraph statistics · heuristic search |
| Difficulty | 50% · Moderate |
Charles Wheatstone designed the cipher. Lord Playfair championed it to officials and gave the system its enduring public name.
Many historical references call it the Playfair cipher, but the technical invention is Wheatstone's. The name reflects dissemination success, not original authorship.
